
Security toolkits can help practitioners to handle the complexity of identifying the risks of crime and terrorism, and to develop appropriate solutions. This page shows two toolkits aimed at security practitioners taking on terrorism and crime:
- The Hostile reconnaissance toolkit (developed with University of the Arts London, and University of Huddersfield)
- The Terrorism/ crime at complex stations toolkit (developed with University of Huddersfield). The glossary developed for the project is here. Run-throughs of toolkit – hostile vehicle attack and theft from retail store within station – are here.
Serious games can help practitioners to learn complex/ dynamic approaches to crime and other problems. This page shows a serious game, designed as a teaching aid for applying the Conjunction of Criminal Opportunity Framework to combat cybercrime. It was developed by Martin Ruskov as part of his PhD research.
Security toolkits
Toolkits can help practitioners to handle the complexity of identifying the risks of crime and terrorism, and to develop appropriate solutions. They can expand the thinking space (provided they are properly designed to avoid rigidity). As with checklists (Sidebottom et al. 2012), they can systematise the sequence of actions in some preventive process (such as the 5Is Framework or SARA), including the search for responses.
If carefully designed and tested, toolkits can take a huge mental load from the user, by guiding them to focus on a sequence of steps, one at a time, customised to the inputs they have already made up to that point regarding scope of problem, context etc. They can also provide a range of drop-down solutions and example responses at each step.

Hostile reconnaissance toolkit
This highly interactive toolkit, based on situational crime prevention principles and expert experience, was developed for the UK Centre for Protection of National Infrastructure by the Design Against Crime Research Centre, University of the Arts London, and the Applied Criminology and Policing Centre, University of Huddersfield.
The development work for this toolkit led us to identify the key sequence of Think perpetrator, think opportunity, think situation, think security, think designer, think manager. It also generated the Ds Framework as a means of leading thinking beyond ‘deter and detect’; and a way of notating crime scripts in terms of location as the perpetrator viewed/researched the site remotely, entered, moved within and left it, and actions/goals at each point.
A presentation on the toolkit describing the rationale and showing the main run-through is here:
Below are some sample slides from this presentation, illustrating some of the steps in the toolkit.
The slide below shows the basic action sequence that users follow as they work through the toolkit:

The slide below, following the perpetrator’s movement script, asks the user to enter characteristics of different parts of their site, that make reconnaissance easier. Illustrative entries are provided in each cell, which users can overwrite with their own input:

Further illustrations of the think perpetrator approach in this toolkit are in the page on scripts and script clashes.
The slide below shows the menu of response alternatives to help users choose interventions appropriate for a given zone of their site, and for the perpetrator’s position relative to that zone (e.g. entering it). The grey options at the top describe possible interventions in terms of the D principles for influencing perpetrators, with drop-down descriptions of each. The blue options at the bottom present users with an alternative discourse in terms of more tangible practical methods. Users may draw on whichever alternative they are comfortable with:

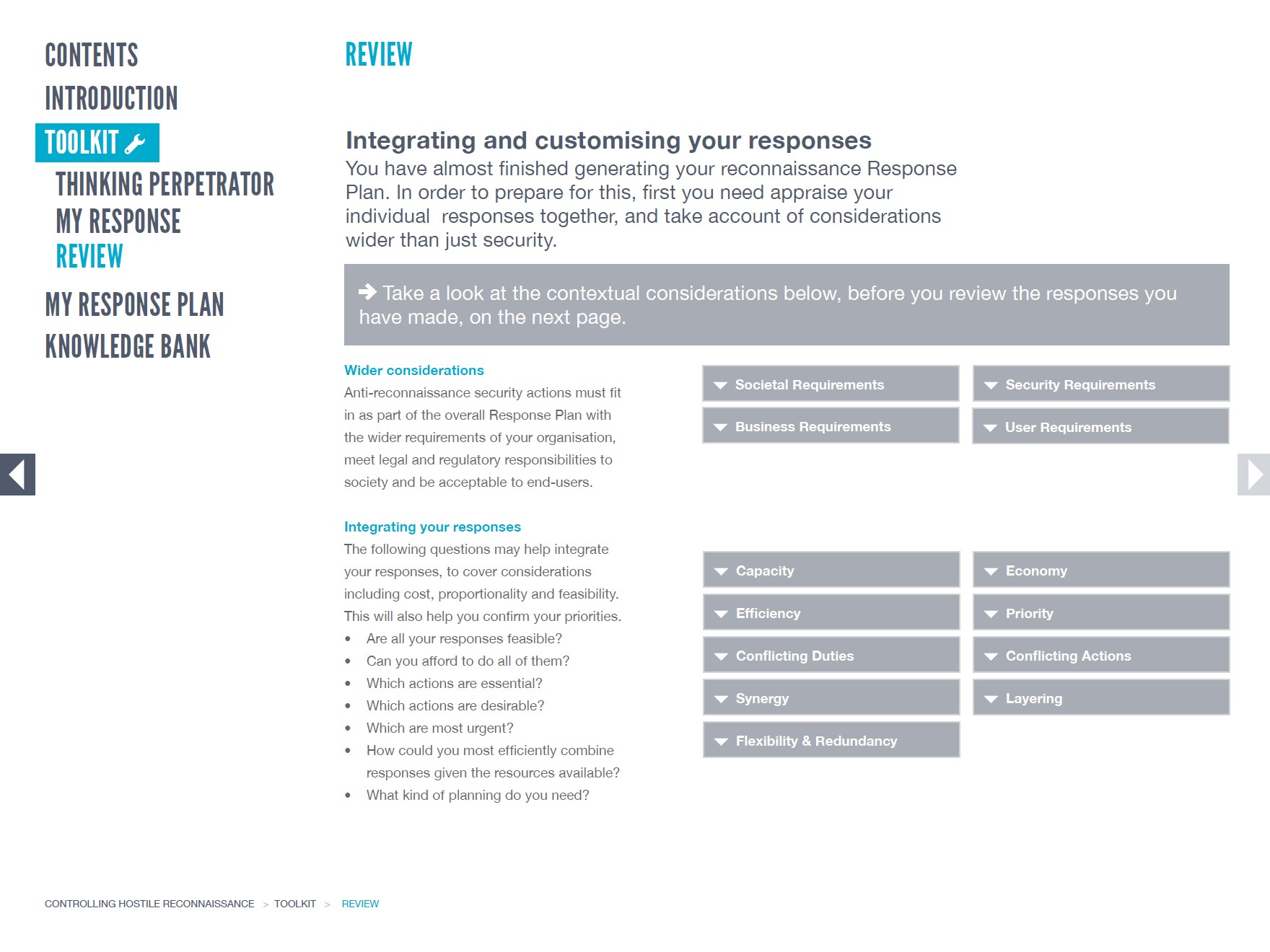
The image below shows how the toolkit user, having come up with one or more candidate intervention methods against hostile reconnaissance, is guided to shift from ‘think security’ to ‘think designer’. This means selecting and/or modifying the ‘raw’ interventions so they not only boost security, but also avoid, or at least minimise, undesired side effects such as social exclusion, interfering with business, and user-unfriendliness.

Terrorism and crime at complex stations toolkit
The Directorate-General for Mobility and Transport of the EU (DG-MOVE) contracted the Applied Criminology and Policing Group of the University of Huddersfield to develop, initially, an outline toolkit for preventing and responding to terrorist attacks at complex, multi-modal train stations (those with metro, bus and other connections). This was to be based on a review of academic literature, grey literature, interviews with security managers and site visits across the EU.
One of the challenges was the sheer number of possibilities to handle – around 12 attack methods x 12 target types x 12 weapon types. The other was how to supply the best possible guidance in the absence of terrorism-specific evaluations of what-works. Our approach relied heavily on transfer of tested theoretical principles from situational crime prevention.
DG-MOVE then awarded the University of Huddersfield team a second contract to turn the main elements of the outline into a full-blown interactive toolkit, specifying the use of the 5Is Framework, the capability of customisation to local sites and contexts, and the use of multiple EU languages. However, while the Implementation and Involvement tasks of 5Is were developed for the outline toolkit, for reasons of time/cost they were not covered for the interactive version. That is a job still to be done, if anyone is interested in supporting it!
Phase 1 – including outline toolkit
A presentation on the outline toolkit is here:
Below are some sample slides from this presentation, illustrating the thinking and research behind the toolkit.
The slide below shows the underlying logic of Phase 1 of the toolkit project. In the absence of a body of knowledge derived from rigorous ‘what works’ evaluations of counter-terrorist interventions, the team developed a ‘conceptual attack framework’. This brought together what was known from a range of ‘softer’ sources, including a literature review, fieldwork visual audits of stations and interviews with station security staff, and combined this with the transfer of tested principles from situational crime prevention. The project deliverables included a ‘security action knowledge tree’, organising what the sources revealed, and an outline, text-based toolkit, which was to form the basis of the interactive version in Phase 2:

The slide below shows the conceptual attack framework in more detail. The left column shows a listing of terrorist attack methods (e.g. hostile vehicle ramming), weapon types and target types (e.g. station infrastructure, passengers). The middle column shows a generic attack script covering a range of action alternatives. The right column presents the findings from fieldwork and a Realist review of the literature. These findings were organised on the security action knowledge tree, which itself was derived from the Conjunction of Criminal Opportunity (covering causes and interventions) and the 5Is (covering process know-how, e.g. on implementation) frameworks; and the discourses of environment and architecture in the CPTED ontology:

More on the attack procedure is here.
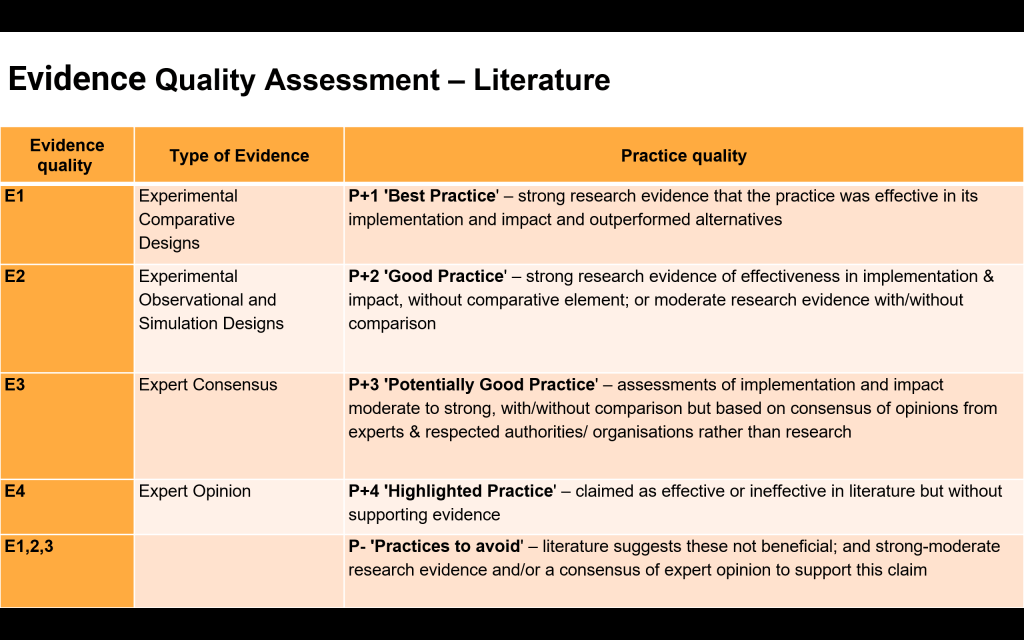
The slide below shows the evidence quality assessment scale that the team developed, to handle findings that ranged from rigorous (by far the minority of cases) to the weak; and those practices to avoid. (An equivalent scale was developed for the fieldwork evidence.) It was judged necessary to include the weaker sources, with due caution, because users cannot wait for the research shopping list to be complete, but have to have access to the best knowledge available at the time:
The slide below shows how the findings of the review were extracted from the text of the report as ‘one-liners’ and organised on the security action knowledge tree part of the Conceptual Attack Framework (CAF). This enabled ‘like findings to be put with like’. Each finding came with a reference link to its full entry in the main report, and its evidence equality assessment rating (see previous slide):

The slide below summarises the overall journey of users in working through the toolkit, in terms of leading them through a sequence of different perspectives:

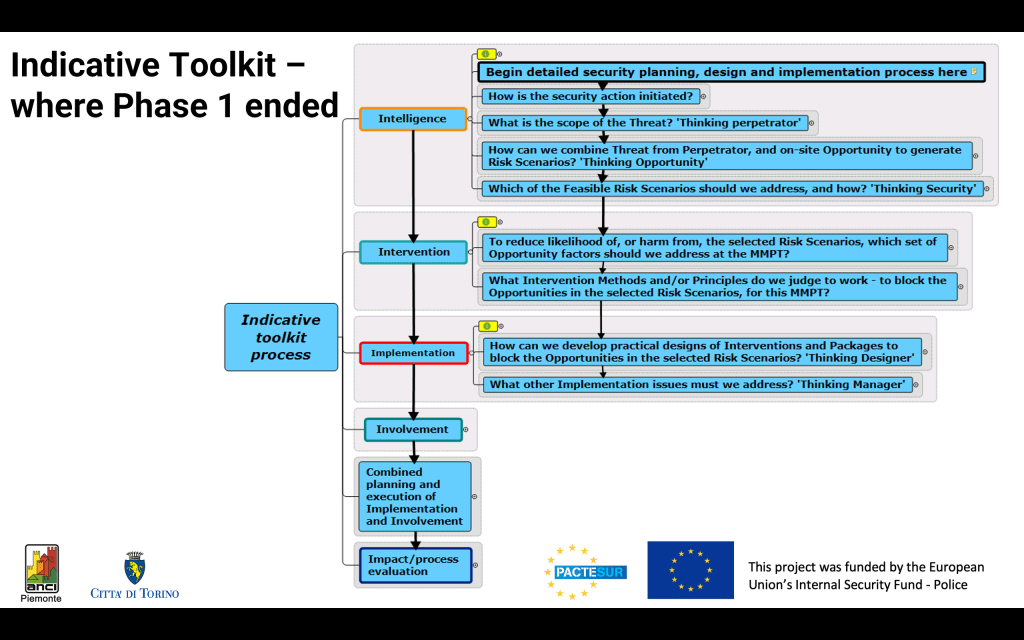
The slide below shows the outline, or ‘indicative’, toolkit as delivered from Phase 1 of the project. Much of the detail is compressed into collapsed boxes. It shows the relationship with the 5Is process:

Phase 2 – interactive toolkit
The outline toolkit developed in Phase 1 of the project formed the starting point for developing the interactive version in Phase 2. This presentation describes the process and takes the viewer through the toolkit with a worked example:
The slide below shows the streamlined user action sequence developed for Phase 2 – the interactive toolkit:

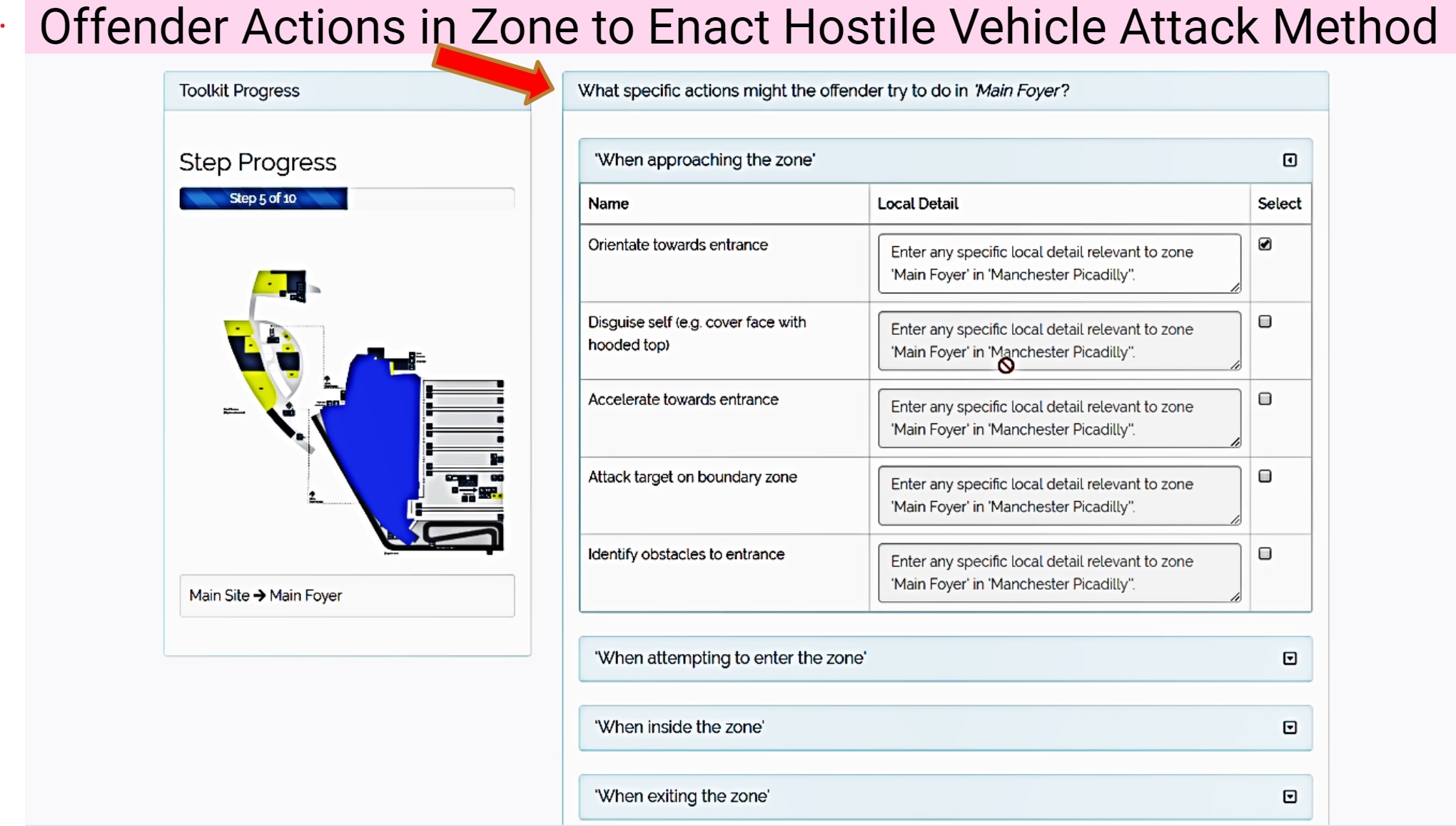
Below are some examples of the interactive screens. Users can upload a map of their site into the toolkit and select one zone at a time to consider, for one kind of attack method – in this case, the main foyer, and hostile vehicle ramming. The toolkit customises the rest of the sequence to this method.
The first slide below asks users to think about the kinds of action (or crime script) the offender might take in orientating towards the zone entrance, disguising their intentions, accelerating towards the entrance and so on. It repeats for entering the zone, moving within it and exiting. In each case users can enter free-text local detail:
The slide below illustrates the switch from ‘think perpetrator’ to ‘think environment’. Here, users are asked to identify ‘risk attributes’ of the zone, that make the above-identified actions more likely, that is, more rewarding, less risky and less effort for the offender:

The slide below shows how users of the toolkit are guided to select security actions to reduce the risk attributes in the zone and counter the offenders’ actions, from a menu customised to those actions, previously identified by the users:

The slide below shows a summary of a single session, in which the toolkit user focuses on one attack type (e.g. terrorism), one method (e.g. hostile vehicle ramming) and one zone (e.g. main foyer). (The session is repeated for different attack types and methods, and different zones.) The summary amounts to an action list for the security staff and senior management at the station:

Glossary for terrorism/crime at complex stations toolkit
A glossary was developed for this toolkit.

Further information on the terrorism/crime at complex stations toolkit
Full project team (University of Huddersfield): Rachel Armitage, James Bray, Kris Christmann, Paul Ekblom, Alex Hirschfield, Eloise Keating, Leanne Monchuk, Andrew Newton, Simon Parkinson, Michelle Rogerson and Daiyaan Shreef.
Run-throughs of toolkit – hostile vehicle attack and theft from retail store within station – are here.
Enquiries about obtaining the toolkit – currently for official bodies in EU Member States only – to: MOVE-EU-LANDSEC@ec.europa.eu cc eucpn@ibz.eu
It may however be possible to produce non-EU versions – if interested, contact.

Serious game: teaching the Conjunction of Criminal Opportunity Framework
Serious games can help practitioners learn complex/dynamic approaches to crime and other problems. They can also be engaging and motivating, especially if they allow for multiple players.
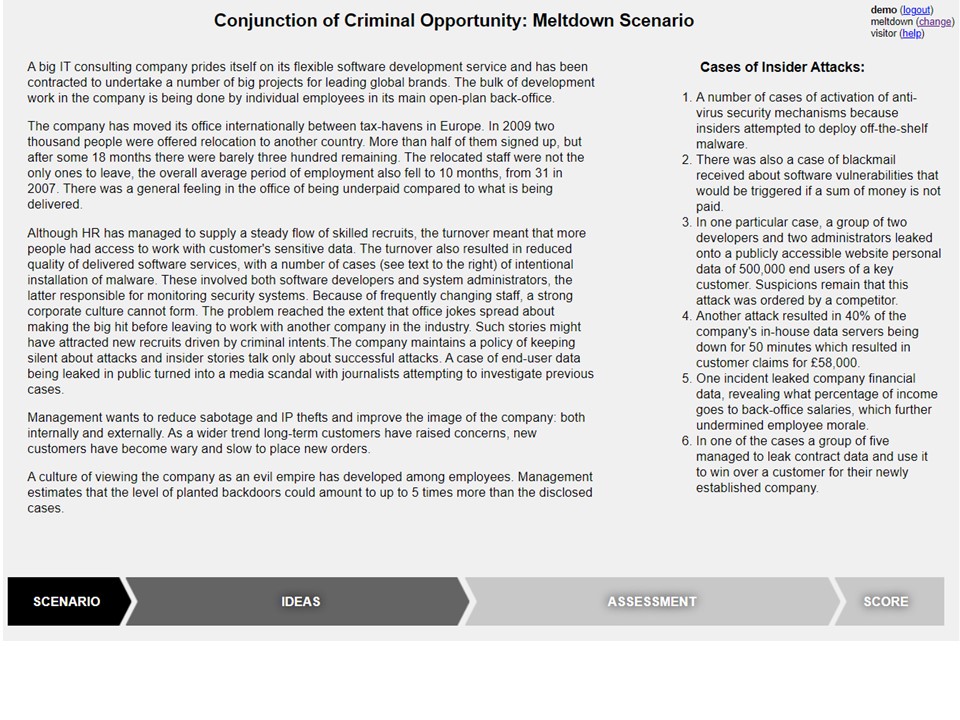
An experimental interactive ‘serious game‘ for training cybercrime practitioners in the application of the Conjunction of Criminal Opportunity Framework, was developed for Martin Ruskov’s PhD thesis at UCL. It is described here and in these articles (Ruskov et al. 2012, 2013, 2014, 2022 – the last is an evaluation). The game enables multiple players, working with set crime scenarios (e.g. cybercrime insider threat, phishing attack), to first take the point of view of the security side and generate proposals for interventions, and then to flip perspectives and ‘think offender’ in order to critique them. Alternatively, red and blue teams could propose and critique one another’s interventions. Here are example graphics from the game.
One of the scenario screens is below.
The idea generation screen below is based on the CCO Framework’s causes diagram. It features semi-structured input dialogue for participants to suggest proposals for intervention, and visual feedback for identified ideas:

The toolkit screen below asks participants to think whether their proposed interventions could influence other causes, beyond the one that they originally designed it for. This reflects the many-to-many relationships between intervention methods, intervention principles and causes:

An example of an assessment screen is below. Here participants are asked to assess how interventions will affect success estimations by offenders:

The final score screen is below. In the upper part of the screen are score and ranking. When a participant hovers with the mouse over an individual assessment of an idea, a pop-up with the comments given to this assessment appears:

Video run-through and working version of game
A video run-through of the game is here. A working version of the game is here.